New Best Practices for Passwords
Creating a hard to crack password has been similar to creating a witchcraft spell – upper and lower case letters, numbers, special characters, with the eye of a newt thrown in for good measure (does anybody know what a newt is?). But now the National Institute for Standards and Technology (NIST), who created those original best practices, have changed their minds. They’ve come up with a brand new approach to creating passwords that incorporates easy to remember words (for you) that should also be hard to crack (for cyberthieves). That’s the good news. The bad news is that not all websites and applications have adopted these new recommendations, so it will take some time before you’ll be able to utilize this knowledge. But we want to keep you up to date with emerging trends.
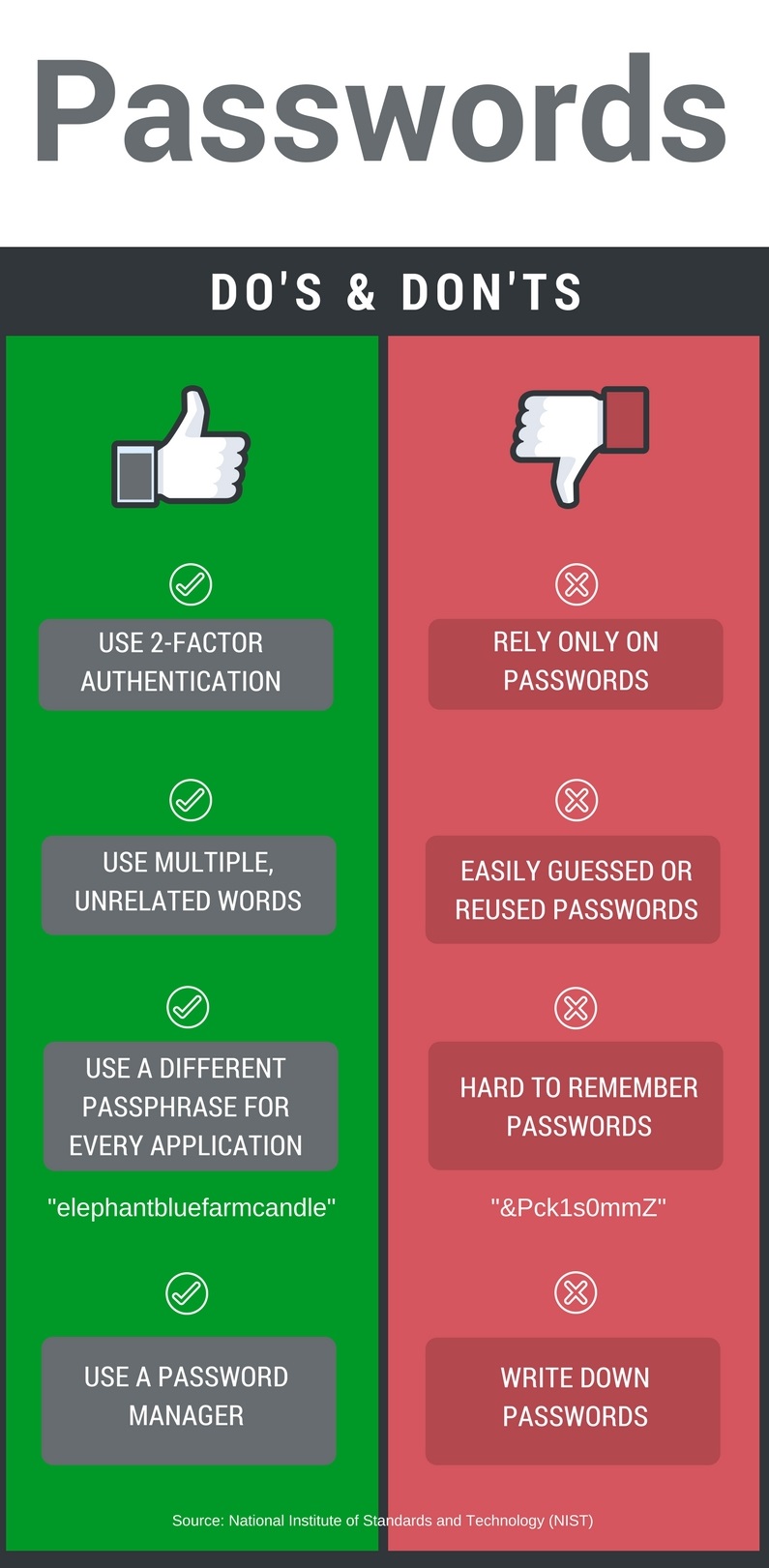
These new passphrases should incorporate unrelated words, like kitchenletterfoot, or puppypaintsalt. They should be long and nonsensical, making them hard to guess but hopefully easy to remember.
There are other changes coming soon to your login procedures. NIST recommends that those handy password hints, like your mother’s maiden name and the street where you grew up should be eliminated, because social media has eliminated all our secrets. They also say that commonly used passwords should be forbidden (we’re talking to you, Password123).
Another surprising recommendation in the new guidelines is to lift the requirement that passwords be changed frequently, like every 90 days. Turns out, people usually just make one small change to their existing password to renew it for the next 90 days, which really doesn’t make it any stronger.
And here are some letters and numbers you should pay attention to – 2FA, standing for Two-Factor Authentication. This is the practice of having something you know (like your password) combined with something you have (like your cell phone). You do this all the time when you use your debit card – you have the card and you know your PIN. NIST strongly encourages using 2FA whenever it’s available.
The folks at NIST think that easier passwords will make it more likely that users will take proper precautions. No cauldron required.